Payment Hardware Security Modules (HSM) are the unsung heroes playing a crucial part in securing the payments ecosystem. Their use is mandated by the Payment Card Industry Security Standards Council (PCI SSC) to provide high levels of protection for cryptographic keys and customer PINs (Personal Identification Number) when issuing and processing card payments.
For years, issuers and acquirers have been buying and managing payment HSMs in their own, on-premise data centres, alongside payment applications. However, payment HSMs are expensive to run, need regular upgrading, and until now have been one of the barriers to adopting public cloud. Unsurprisingly, the winds of change are in the air.
The unique key management requirements combined with physical and device lifecycle security controls means public cloud providers don’t (yet) offer Payment HSM-as-a-Service. Building a Payment HSM-as-a-Service offering requires a hybrid approach that borrows some techniques from the public cloud providers’ playbook, while maintaining the hardware in private data centres.
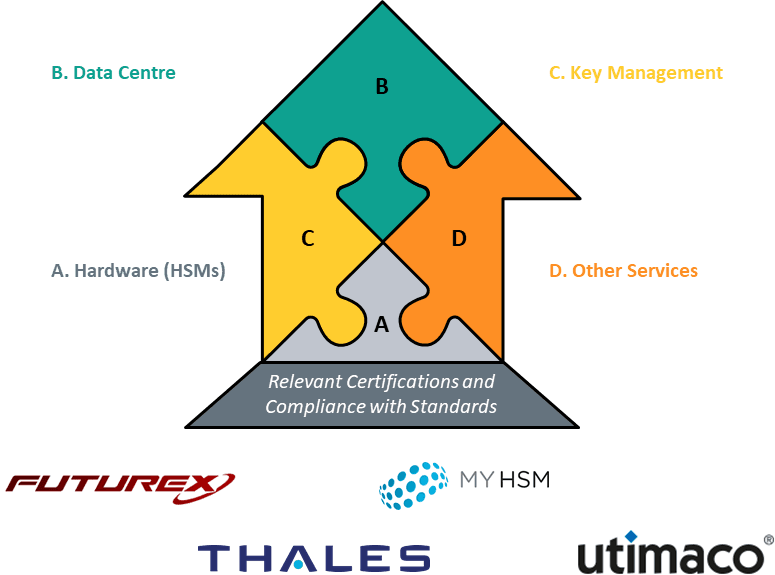
After introducing the basics and outlining the imperative for change, Celent profiles the key Payment HSM-as-Service providers and their offerings: Futurex, MYHSM, Thales, and Utimaco. We spoke to each of the players and wrote the profiles based on those conversations and the materials shared by the providers. Given that the space is relatively new, this is not an evaluation and comparison of each solution. The profiles are presented alphabetically; the order does not imply Celent’s judgement on the solution.
Clearly, players in the payments industry are no longer shackled to running scores of payment HSMs in their own data centres; they have alternatives. Change, while necessary and inevitable, is not going to happen overnight. We conclude with Celent’s perspective on the pathways to Payment HSM-as-a-Service adoption.