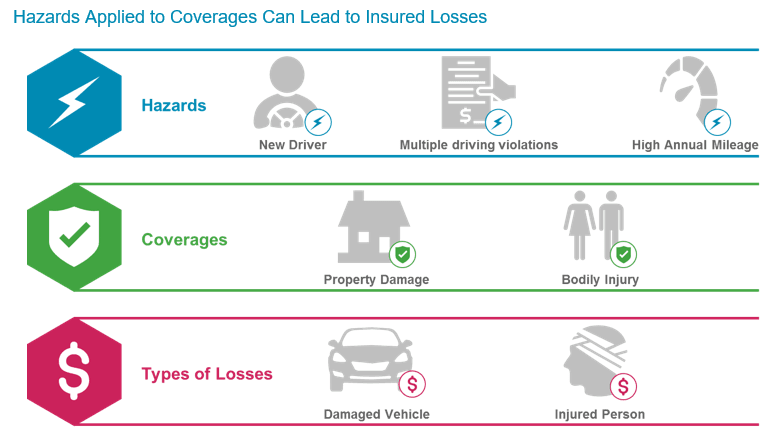
保険会社が成功するには、損害の確率を正しく見積もる必要がある。そのため保険会社は、損害の確率を上げるリスクおよびその他の要因についての情報を収集する。長年にわたり、そのような情報の収集は手作業で行われてきた。
しかし、状況は変わりつつある。保険会社は、リスク評価を自動化する新しいテクノロジーを活用して、損害確率の予測を向上している。
これらの新しいタイプの危険要因の特徴としては、意図的に組織および個人に損害を与えようとする悪人が含まれているということである。
サイバー損害は3つのカテゴリーに分かれる。すなわち、アファーマティブ、サイレント、ダイレクトである。3つの大手サイバー保険会社のアファーマティブ補償、裏書条項、および侵入工作対応サービスの例が示されている。